Latest Gear Live Videos
Chrissy Teigen Slams Jennifer Lopez’s Entourage

Posted by Andru Edwards Categories: Music, Rants,


John Legend's fiancee has lashed out at Jennifer Lopez's uptight security team. Top model Chrissy Teigen claims she was asked to stop watching John perform at the Sound of Change concert in London on Saturday night and leave the side of the stage by the "Dance Agai"' singer's team before Jennifer's "supreme arrival."
The 27-year-old beauty vented her frustration in a furious rant on Twitter, writing, "I won't get into it but Jennifer Lopez' people need to calm the f*** down. I love Jennifer Lopez. But as I am sitting and watching John perform, I don't need her people to lay down the j-lo laws."
Click to continue reading Chrissy Teigen Slams Jennifer Lopez’s Entourage
Advertisement
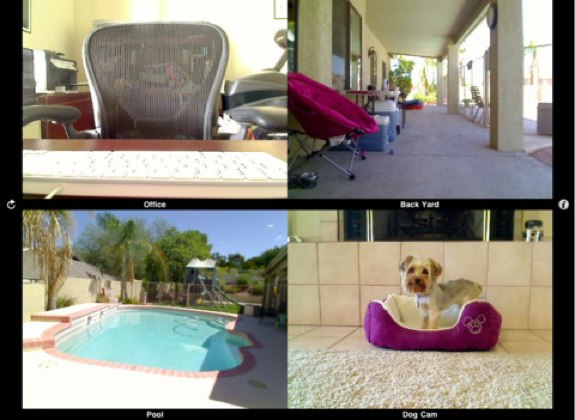
iCam video security app now supports 256-Bit AES encryption & iPhone 5

Posted by Jason Diaz Categories: Utilities, App Updates, $4.99,
Video security surveillance app maker, SKJM, has updated its iCam app to version 2.2 and added some useful features. iCam now supports 256-Bit AES encryption, motion event image thumbnail gallery style, and supports the iPhone 5 4-inch display size. The update also includes various bug fixes and optimizations. I highly recommend this invaluable app. iCam has motion detection functionality sent via push notifiation alert with support for a bevy of third-party of security surveillance cameras. iCam is universal binary iOS app. Most notable feature: iCam for iPhone can support up to 12 simultaneous live video streams and the iPad up to 16. Don't don't have it? iCam is priced at $4.99 in the App Store.
What's New in Version 2.2
- Added support for 256-bit AES encryption.
- Added support for Motion Event Image Thumbnails.
- Added iPhone 5 screen size optimizations.
- Fixed various minor bugs.
Be sure to also update the iCamSource application running on your computer(s) to the latest version: http://skjm.com/icam/support.php
Read More  | iCam
| iCam
Rihanna Hires Extra Security

Posted by Andru Edwards Categories: Music,
.jpg) Rihanna has hired extra security to protect her. The "Stay" singer - who obtained a restraining order against an obsessed fan last week after he broke into her neighbor's home, which he mistook for the 25-year-old popstar's property - was spotted with five new bodyguards while leaving a Los Angeles nightclub on Saturday.
Rihanna has hired extra security to protect her. The "Stay" singer - who obtained a restraining order against an obsessed fan last week after he broke into her neighbor's home, which he mistook for the 25-year-old popstar's property - was spotted with five new bodyguards while leaving a Los Angeles nightclub on Saturday.
According to gossip website X17.com, the star was flanked by the burly men as she enjoyed a girls' night out at Playhouse without her boyfriend Chris Brown.
Her beefed up security team comes after she was assaulted upon leaving a London nightclub last month and forced to seek medical attention.
The singer was targeted in an unprovoked attack by a man, who hurled a bottle of Lucozade at her, while she was leaving exclusive nightclub The Box with her model pal Cara Delevingne. The force of the glass bottle caused the Barbados native to fall and cut open her knee. Her bodyguard's leg was also said to have been injured as he attempted to catch her attacker, who allegedly shouted something about her boyfriend Chris before throwing the bottle at her.
Adobe releases flash patch to counter malware attacks on OS X and Windows
Posted by John Kilhefner Categories: PC / Laptop, Software,

A new patch by Adobe Systems fixes the two Flash player vulnerabilities currently under attack. The attacks install malware and targets both Macs and PCs. The targets all seem to be Flash versions for OS X and Windows. The patch, however, is also available for Linux and Android.
The exploits target Safari as well as Firefox, of which the vulnerability is classified as CVE-2013-0634. The vulnerability is also reportedly tricking Windows users into opening Word documents containing the Flash content.
The bug, according to Adobe, was discovered by members of the Shadowserver Foundation, Lockheed Martin's Computer Incident Response Team and MITRE.
Read More  | Adobe via Ars Technica
| Adobe via Ars Technica
Samsung Galaxy S III, other Android devices susceptible to malware through Google Play
Posted by John Kilhefner Categories: Smartphones, Google, Software,

A "severe vulnerability" has been identified within the Samsung Galaxy S III, Galaxy S II, Galaxy Note II, and possibly other Android devices.
The vulnerability leaves these devices open to malware downloaded in remote apps, which can then read user data and even brick your phone completely. "The good news is we can easily obtain root on these devices and the bad is there is no control over it," said xda-developers user Alephzain. Usually, vulnerabilities like this require physical access to the phone, while this vulnerability allows it to be attacked from apps downloaded from the Google Play Store.
Samsung is apparently aware of the problem, but has not publicly acknowledged the problem. Millions of devices are reportedly at risk right now as public knowledge of the issue spreads.
Read More  | The Verge
| The Verge
Skype patches recovery password vulnerability

Posted by Jason Diaz Categories: Corporate News, Microsoft, Software,

Microsoft, the parent company of Skype, has patched a password recovery tool bug that Russian hackers utilized to exploit and gain access to user's accounts with nothing more than their account name and email. According to The Next of Web, they independently verified the five step process and confirmed that it works. Skype made this announcement on its website blog:
Early this morning we were notified of user concerns surrounding the security of the password reset feature on our website. This issue affected some users where multiple Skype accounts were registered to the same email address. We suspended the password reset feature temporarily this morning as a precaution and have made updates to the password reset process today so that it is now working properly. We are reaching out to a small number of users who may have been impacted to assist as necessary. Skype is committed to providing a safe and secure communications experience to our users and we apologize for the inconvenience.
Read More  | Skype
| Skype
French authorities nab Android Trojan horse maker

Posted by Jason Diaz Categories: Google, Misc. Tech, Mods / Hacks, Software,

Yet another case of malware found on Google Play. A 20-year-old man suspected of an elaborate Android Trojan SMS scheme was arrested in France. The alleged hacker tallied over 17,000 Android users that installed malicious software posed as copy cat apps. The scheme works by sending SMS messages at a premium cost. The hacker then earns a micro-transaction fee, leaving the unsuspecting user with an unexpected hefty monthly bill.
The hacker informed French authorities that he was more motivated by the technical aspect than monetary gain and had goals of becoming a software engineer. Cyber criminals have made inroads into making malware in the Android platform partly because the Google Play Store is open and is not curated and vetted for security like Apple's App Store. Hackers have created clone malware of popular apps like Skype, Instagram, and Angry birds. Some of these apps steal personal information and passwords and can capture pretty much anything you type.
Computer venders Security, like Sophos, strongly advise Android users to be vigilant and also install their free anti-virus security suite.
Read More  | The Register
| The Register
Apple granted patent that can disable your iPhone 1984-style

Posted by Jason Diaz Categories: Apple, Smartphones, Corporate News,
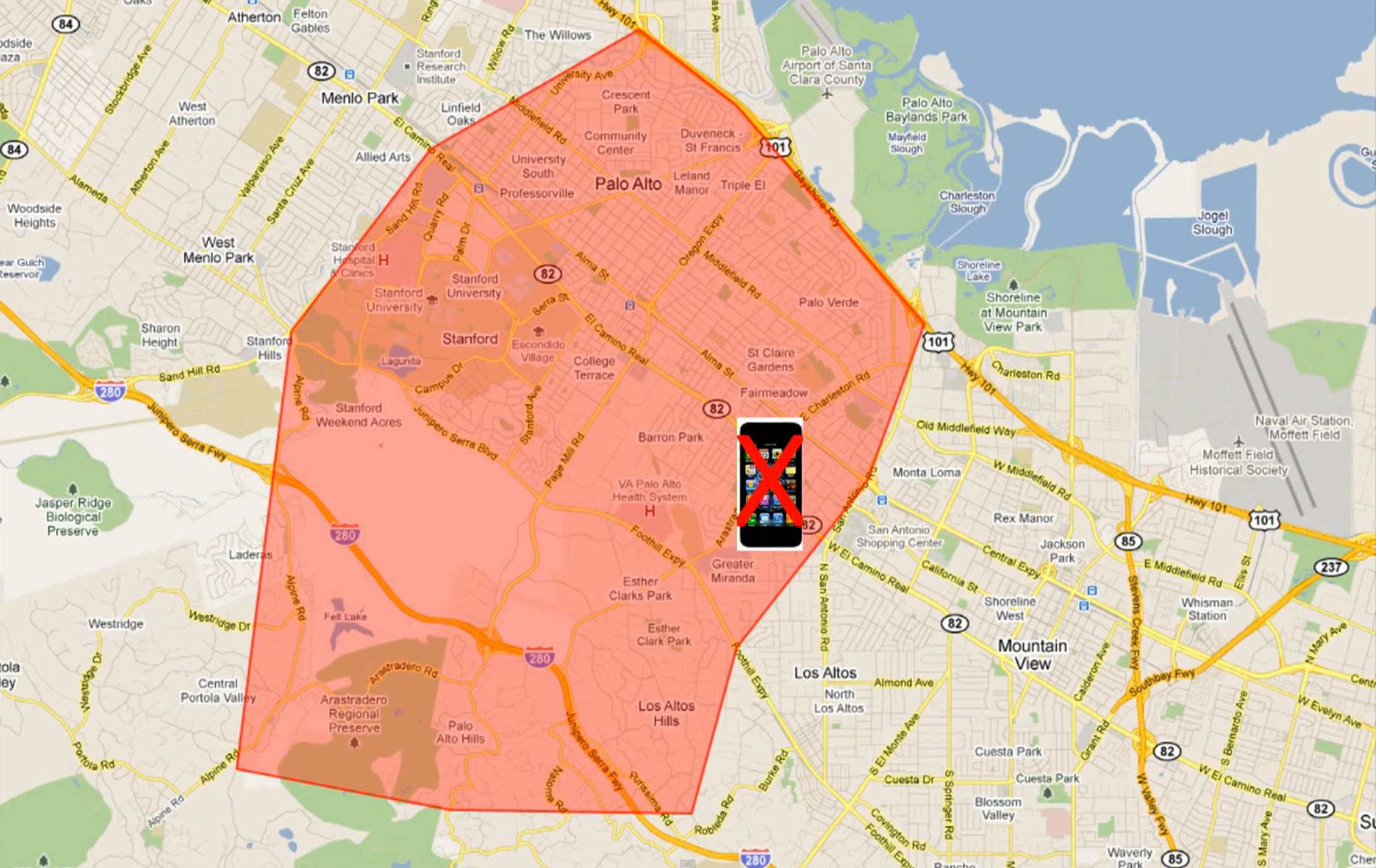
Apple is not shy about submitting patents on its creations, but this one is a little different. This particular filing attempts to patent the essence of 1984, and would give the Cupertino-based company the sole right to disable a user's iPhone camera app in restricted areas, such as at a concert venue or movie theater. However, it appears that the now-granted patent may disable far more than just your ability to take snapshots.
Click to continue reading Apple granted patent that can disable your iPhone 1984-style
Read More  | Business Insider
| Business Insider
Apple, Nokia, and Google Map security brouhaha: fact or hype?

Posted by Jason Diaz Categories: Apple, Corporate News, Design, Editorial, Features,
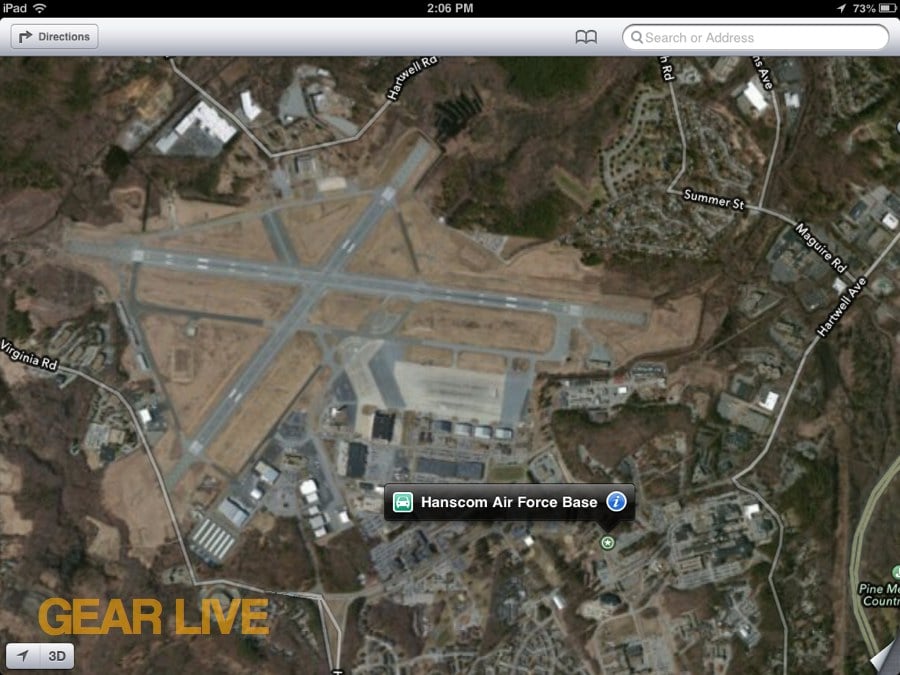
In the latest Apple Maps saga, The Verge is reporting some security concerns regarding sensitive military installations that appear on mapping solutions by Apple. as compared to Google Maps and Nokia Maps. The picture being portrayed is that Apple is showing more information than the other companies. While it may appear accurate on the surface, it lacks transparency and fairness. Case in point, we all can agree that Area 51 is one of the most secretive government military installations in the world. Coincidentally, or ironically, The Verge failed to report that Google's map offering shows a much more pristine image of Area 51 than Apple's map of that particular base, nor is it pixelated for security. I went out of my way to tweet the author of the post to get an explanation for the discrepancy. There are definitely more examples of similar discrepancies, this isn't limited to just Area 51.
Read More  | The Verge
| The Verge
Gallery:
ABC News tracks stolen iPad to home of TSA agent

Posted by Jason Diaz Categories: Apple, Corporate News, Handhelds, Videos,

We can't stress enough the countless stories that highlight the benefits of having the Find My iPhone app installed on your iPhone, iPad, iPod touch and enabling Find My Mac on Apple computers, allowing you to track their whereabouts through iCloud. ABC News investigates and finds at least 400 TSA screeners who left, or were fired, after allegations of theft in the workplace. In the video below, ABC tracks down a stolen iPad, sting-operation-style, to a TSA agent's home with the use of Apple's free tracking service. The agent is caught on video and has the audacity to throw his wife under the bus, saying it must have been her that took it. The TSA Agency has come under fire in recent years and continues to find new ways to be in the news, obviously for the wrong reasons.
Click to continue reading ABC News tracks stolen iPad to home of TSA agent
Advertisement
© Gear Live Inc. {year} – User-posted content, unless source is quoted, is licensed under a Creative Commons Public Domain License. Gear Live graphics, logos, designs, page headers, button icons, videos, articles, blogs, forums, scripts and other service names are the trademarks of Gear Live Inc.