Latest Gear Live Videos
Los Angeles Judge Orders Defendant to Unlock iPhone with Fingerprint

Posted by Jason Diaz Categories: Apple, Smartphones, Corporate News,
The Apple encryption battles continues! Despite Apple coming up on top when the FBI and the DoJ’s petition to unlock the infamous Bernardino iPhone was withdrawn, a new brouhaha has commenced. A court order has been filed by U.S. Magistrate Judge Alicia Rosenberg mandating that Los Angeles defendant, Paytsar Bkjchadzhyan, unlock her iPhone by placing her finger on the Touch ID’s home button.
Click to continue reading Los Angeles Judge Orders Defendant to Unlock iPhone with Fingerprint
Read More  | LA Times
| LA Times
Advertisement
Supreme Court to drop the hammer on Internet threats

Posted by Ariel Levin-Waldman Categories: Corporate News, Internet,

Anyone who has spent any time online has probably gotten a death threat or two. Maybe you were playing Call of Duty and some 11-year-old questioned your sexuality before telling you he'd kill your family. Maybe you offended the legions of desperate Tumblr bloggers in some arcane way and you woke up to a swarm of messages on your dash saying they would hack you and your dog apart with rusty machetes. You probably did what any reasonable person did and rolled your eyes and went about your day.
Statements and threats on the internet aren't usually taken seriously. Both the giver and the receiver are usually anonymous and the threat is usually over the top enough that you laugh and think nothing of it.
Well, the highest court in the United States might be ready to have the final word.
Click to continue reading Supreme Court to drop the hammer on Internet threats
Watch this: Tim Cook & Apple Senate testimony

Posted by Andru Edwards Categories: Apple, Corporate News,
Apple CEO Tim Cook and CFO Peter Oppenheimer are appearing before Senate today to address the methods Apple uses to determine how it pays taxes in the US and abroad, and you can watch everything happen live over at C-SPAN. Hit the link below!
Read More  | C-SPAN
| C-SPAN
McCain’s Television Consumer Freedom Act calls for a la carte TV, end of sports blackouts

Posted by Jason Diaz Categories: Corporate News, Home Entertainment, Videos,
Speaking of TV, Republican US Senator, John McCain, of Arizona has introduced a bill to the house floor dubbed The Television Consumer Freedom Act of 2013. The legislation has three components. The first is the unbundling of TV programing from content and cable companies, which allows the consumer to have à la carte service options. It also lets the consumer pay for only those channels and shows they want to watch. The second will establish consequences for providers that misuse or don't properly execute the stipulations in the bill, such as downgrading their online offering. Lastly, it will eliminate local sports blackouts, finally!
All politics aside, every consumer should get behind this bill. Perhaps an indirect benefit for content makers is that the bill could help curb privacy, which is running rampant, although many do not admit so publicly. In the end, if done right, the bill could break the cable provider's stronghold on the traditional content distribution model, eliminate the exorbitant pricing scheme, or, as the Senator of Arizona eloquently put it, end the cable monopoly. As I'm writing this, a tear rolled down my eye. Thank you Mr. John McCain for thinking of my wallet. Watch the historical speech after the quick break.
White House responds to petition, says cell phone unlocking should be legalized

Posted by Jason Diaz Categories: Smartphones,
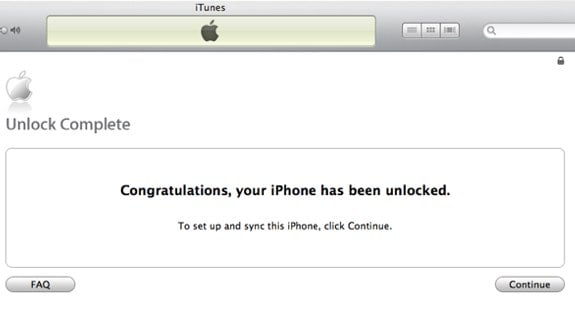
It started as a petition needing only 100,000 signatures requesting that the White House make an official response to the right of cellphone owners to lawfully unlock their cellphones. The Library Of Congress deemed unlocking one's cellphone illegal in October 2012; a ruling that would take affect in the new year. Now, the White House has officially announced that they too agree with the 114K petitioners. It recommends that cellphones be unlocked as long as the customers first meet their carrier's contractual agreement. The White House has even included tablets to the list of devices. Consequently, the Library of Congress has agreed and support the review their policy, which was strongly urged by the FCC.
"The White House agrees with the 114,000+ of you who believe that consumers should be able to unlock their cell phones without risking criminal or other penalties. In fact, we believe the same principle should also apply to tablets, which are increasingly similar to smart phones. And if you have paid for your mobile device, and aren’t bound by a service agreement or other obligation, you should be able to use it on another network. It’s common sense, crucial for protecting consumer choice, and important for ensuring we continue to have the vibrant, competitive wireless market that delivers innovative products and solid service to meet consumers’ needs." - White House Administration
Read More  | White House
| White House
Australian courts overturn ruling the ACCC brought against Google
Posted by John Kilhefner Categories: Corporate News, Google,

Six grueling years of the ACCC dragging Google in and out of Australian courtrooms and hearings for "misleading advertisements" displayed in search results have now come to an end.
Five Australian High Court judges have overturned a ruling requiring Google to set up programs that properly vet ads. The lawsuits started because of the specific claim that if one were to search Google in 2006 for "Honda Austrailia," the user would also be shown sponsored ads from competing car companies. This new ruling, however, proves that the concern of the ACCC is an outdated one.
Read More  | Reuters
| Reuters
$2.1 million in Wii U consoles stolen in Seattle heist

Posted by Jason Diaz Categories: Corporate News, Culture, Nintendo, Wii U,

Tis the season for stealing! No, what? 7,000 Nintendo Wii U consoles were nabbed from a SeaTac Seattle Air Cargo warehouse on Saturday night. Get this--the getaway vehicles were two semi trailers. The burglars managed to use forklifts to steal the pallets of the gaming consoles. It is speculated that it was an inside job. Police authorities are on the lookout for two semi trailers with the branding logo of McKinney. However, more likely than not, these will end up on internet sites such and Craigslist and eBay. Considering that each unit costs $300, it's not crazy to say that the thieves walked away with roughly 2.1 million dollars. Like they say, it's the most wonderful time of the year!
Click to continue reading $2.1 million in Wii U consoles stolen in Seattle heist
Read More  | ABC News
| ABC News
Samsung drops European injunctions against Apple
Posted by John Kilhefner Categories: Apple, Smartphones, Corporate News,

Samsung announced its intentions to drop its injunction requests against Apple. The injunction was for "standards-essential patent infringement" in Europe.
Here's what Samsung had to say:
"Samsung remains committed to licensing our technologies on fair, reasonable and non-discriminatory terms, and we strongly believe it is better when companies compete fairly in the marketplace, rather than in court. In this spirit, Samsung has decided to withdraw our injunction requests against Apple on the basis of our standard essential patents pending in European courts, in the interest of protecting consumer choice."
Click to continue reading Samsung drops European injunctions against Apple
Read More  | The Verge
| The Verge
$1.5 million worth of iPads stolen from JFK Airport

Posted by Jason Diaz Categories: Apple, Corporate News, Handhelds,

Heard of the Capper that nabbed 1.5 million worth of iPads from John F. Kennedy Airport? Coincidentally, the heist happened in the same building used in the movie Goodfellas. You can't make this stuff up! If you haven't heard, here's the story:
Right before midnight on Monday the 12th, robbers used JFK airport forklifts to load two pallets of iPads onto a truck. An airport worker, who was returning from break, saw and confronted the group but was unable to stop them. Law enforcement believes this was an inside job. It has been reported that airport worker, Renal Rene Richardson, was arrested as an accomplice for allegedly acting as a look-out. The FBI was tipped off by other workers who reported that Mr. Richardson made inquiries as to where the iPads were being stored and the location of the forklifts. The other suspects remain at large.
Read More  | http://tech.fortune.cnn.com/2012/11/15/appleipad-minis-theft-jfk/
| http://tech.fortune.cnn.com/2012/11/15/appleipad-minis-theft-jfk/
Thief steals smartphone, uploads pics of himself on victim’s Facebook

Posted by Jason Diaz Categories: Smartphones, Internet,

Another example of a thief not understanding technology. A man was arrested for allegedly stealing a fifteen-year-old girl's smartphone at knife point, and then inadvertently uploaded a picture of himself on the victim's Facebook account. According to the girl's police report, she was playing with her younger brother at the playground when two men approached and stole her smartphone. As always, practice "out of sight of out mind" and know your surroundings, as small mobile electronics are high on thieves hit list.
Read More  | WCVB
| WCVB
Advertisement
© Gear Live Inc. {year} – User-posted content, unless source is quoted, is licensed under a Creative Commons Public Domain License. Gear Live graphics, logos, designs, page headers, button icons, videos, articles, blogs, forums, scripts and other service names are the trademarks of Gear Live Inc.